Previously, I've stated that Android has inbuilt telemetry. Well, while that might not be true, Android still makes unwanted connections by default (Network time, captive portal), even with a custom ROM. There are exceptions to these norm, such as /e/, but they're either still in beta. Hence, here's a guide to do something similar to /e/... but with root.
And, for those who'd want to glance at the messy past of this article, here's the archive.
I am not responsible for any bricked device, loss of warranty, or any other problems as a result of following this guide. It's 100% your decision to do this, & I'm only providing the guide.
Other disclaimers include:
Here are some (probably outdated) references relating to this topic as a whole:
These are the necessary stuff. If you haven't downloaded them, please download them before even doing this.
At this point, Magisk's the only viable root solution for root users. If you're using Magisk 22.0, make a copy & rename its .apk extension to .zip.
Closed source, but it just works.
An open source alternative. Not quite recommended since downloads are limited to mobile Telegram client.
Another open source alternative, but not recommended because it could change captive portal provider to Xiaomi's servers.
Generally, all you might need is the Bromite webview module. The F-Droid & microG package is a good addition if you're using any of them. I don't recommend using the full NanoDroid module unless you can modify its installation. By default it'll install various apps you might not want & remove apps you might want to keep.
First off, clean flash your ROM. That way, you can be fully sure that you start with a clean base. Don't forget to backup whatever you can before doing this though!
For the note, you must use ROMs without GApps. Having microG support (inbuilt / prebuilt) is a nice bonus, although not necessary.
From here on out, don't connect to the internet, at least until the AdAway phase.
If you're using a Lineage-based ROM / CarbonROM, you will enter a Setup Wizard upon first boot.
You can set the time & date for your PDA, but you can breeze through the rest of the setup wizard, denying access to telemetry & location access as you go. You can change them later.
Reminder : Do NOT connect to the internet via any means yet.
Time : Enter Settings > System > Date & time. Disable [Use network-provided time]; [Use network-provided time zone]; & [Use locale default], and tune the time settings to match your area's time, if you haven't done so. We're disabling these options as they may trigger questionable connections to a NTP server. Sure, this is inconvienent (especially when you're travelling), & may not affect privacy that much, but you can at least not trust whatever NTP server around not to screw you over.
Questionable apps (Intent Filter Verification Service, for example): Enter Settings > Apps & notifications > See all apps. On the 3 dot menu on the top-right corner, select Show system. Scroll down until you find "Intent Filter Verification Service" app, & select it. Force stop & Disable the app. At this point, I'm unsure what effect this app has on privacy, as it doesn't have an official documentation. However, ladano claims it connects to Go-ogle & Amazon servers.
Telemetry : This part varies by ROMs, and some don't have it. Here's examples of the ROMs that have it & their locations:
Once you've found & select them, untick "enable reporting".
Accessed by entering Settings > Network & internet > Private DNS. Leaving it in Automatic will cause it to connect to random DoT providers.
To disable this, select "Off" & hit Save.
If you have a provider you can trust & you'd like to use their DoT services, select "Private DNS provider Hostname", type in the host name of your choice, & hit Save.
To check whether your PDA is encrypted / not, go to Settings > Security, and see the Encryption & credentials settings. It'll give you the state of its encryption.
References for my devices:
How to encrypt (only for devices / ROMs that do not encrypt by default & can encrypt):
Disclaimer : Encryption used in this settings are FDE, which doesn't work in A11. Consider this part outdated.If you're installing microG as an user-app, you can't use location services, even with the backends activated. In order to do that, simply install microG & FakeStore apks from the file manager.
Alternatively, if you're using NanoDroid, skip this first. Then, after the TWRP stuff, return to this part & set microG up afterwards.
Skip if using Lineage-microG, OmniROM microG, & /e/ since it's prebuilt.
To set up microG, open microG Settings. Enter Self-Check & tap on "System grants signature spoofing permission" & "Play Store (Phonesky) has correct signature" to grant signature spoofing permission for microG & FakeStore respectively (microG 0.2.16 & later).
Boot to TWRP by whatever means provided to you, whether it's using the provided advanced reboot feature, or by holding down some buttons. Depending on the device, the buttons to press vary. Pocophone F1, as an example, boots to recovery by holding Power & Volume up.
For now, we're flashing things in TWRP. Order of action : Debloat (optional) (look at sysapps list) > NanoDroid zip(s) (optional) > Magisk > Custom Kernel (optional) > wipe Dalvik (& cache if available) > Reboot to system.
More information regarding this can be found in the System Apps list.
Flash NanoDroid-fdroid zip in TWRP. If you have flashed a NanoDroid zip, you should wipe Cache & Dalvik (preferably after flashing everything).
Skip if using Lineage-microG since it's prebuilt.
Flash NanoDroid-microG zip in TWRP. If you have flashed a NanoDroid zip, you should wipe Cache & Dalvik (preferably after flashing everything).
By having microG as a system-app, you can use location services.
Skip if using Lineage-microG, OmniROM microG, & /e/ since it's prebuilt.
Flash NanoDroid-BromiteWebView zip in TWRP. If you have flashed a NanoDroid zip, you should wipe Cache & Dalvik (preferably after flashing everything).
For Magisk 22.0 users : Don't forget to rename Magisk .apk file extension to .zip. For example : Magisk-v22.0.apk > Magisk-v.22.0.zip. Also, don't forget to keep the original .apk file, you'll need it later.
Flash Magisk zip in TWRP.
Maximum compatible Magisk version for each Android version:
Flash your custom kernel zip.
Custom kernels don't really grant any privacy boons, but might enhance performance and/or battery life. However, some custom kernels may also replace the default DNS with other provider (such as CloudFlare), so watch out for that.
Wipe Dalvik (on A-only devices, wipe Dalvik & Cache), & select Reboot System.
Now that we're back in system, our first actions are to install our root apps, starting with terminal, AFWall+, SD Maid, & AdAway. If you have microG installed via NanoDroid, go to the microG section & set-up microG.
You can install them later (after the terminal steps), but installing them at this step allows us to skip installing them in their step.
Open the terminal app & type su. Root access should be granted if requested.
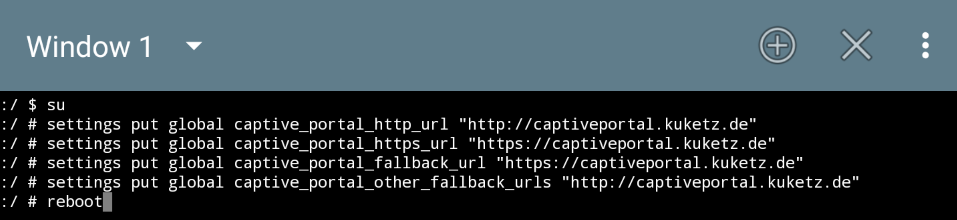
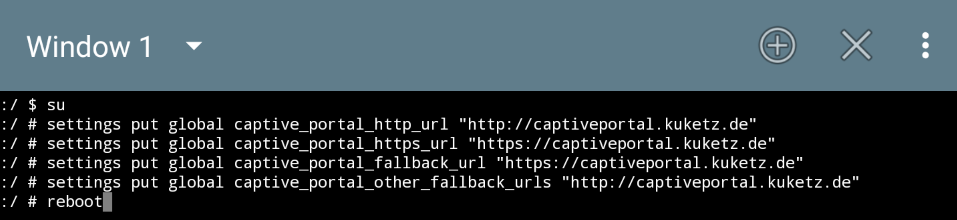
Gain root access in the terminal (skip this part if you just granted microG spoofing permission from terminal). Afterwards, you have 2 choices: to change the captive portal to a more trustworthy captive portal provider, or to disable them altogether.
For those who'd like to use captive portal, first read the captive portal provider list for more information. Then, use these commands:
Output example using Mike Kuketz' captive portal provider: (note : the https in the fallback url part can be ignored)
However, if you're confident that you won't use any Wi-Fi / mobile connections with captive portal, or refuse to use external services for internet connectivity checking, here are the commands:
Output example:
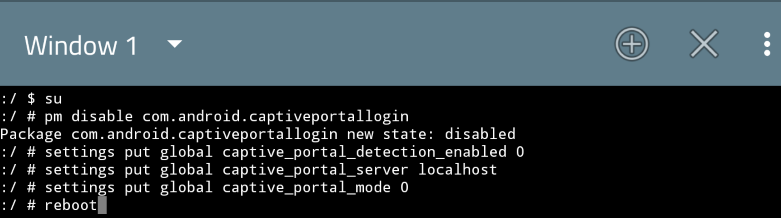
In short, here's what we're doing:
If you're using alternative captive portal & you would like to verify that the setting's applied, here's how :
If you haven't installed AFWall+ yet, please install it first.
Open the AFWall+ app, & it'll immediately ask for root permission. Grant it. Then, to make it easier to block, select the 3 line menu on the right of the search button, and select "Block selected" option. Then, go to its settings menu by selecting the 3 dot button > Preferences.
In the Preferences section, enter UI preferences, untick "Enable notifications" & tick "Show UID for apps" & "Confirm AFWall+ disable". While these changes aren't essential, they kinda make the interface easier to play with. This UI preferences mods can be skipped.
To prevent data leak on boot, go to Preferences > Experimental and select "Startup directory path for script". Then, choose /data/adb/service.d (or /sbin/.magisk/img/.core/service.d/ if using Magisk < 20.4). Afterwards, tick "Fix startup data leak".
Also, in the Preferences > Rules/connectivity, check that IPv6 support is enabled. If not, enable it.
The PDA will still finely connect to the network, even if this is blocked. While it's technically safe to block all of its connections, doing so will prevent captive portal from functioning (at least that's how it is in Pie). How to mitigate that is discussed in the next section.
If you're using network-based geolocation service, you might not want to block this. However, in my experience (with systemized microG, Mozilla UnifiedNLP, Nominatim), I blocked it & location services still works, though only on Wi-Fi.
Block if not using ADB over wireless connection.
You can block connections for this, but only if you disabled captive portal in the terminal section. Otherwise, follow the next section.
No idea what this does, block all of its connections. Found in A10 & A11.
Block all of its connections.
Block all of its connections, if you're not using automatic time adjustments.
You can safely block all of its connection if not using the PDA as a phone. If you plan on doing so, at least leave the mobile data unblocked.
I don't know who prints stuff from their PDA, but, for those who don't, block all of its connections (that is, if it's available & not removed).
Skip this step if captive portal is disabled in the terminal step, or if you don't want to type in the scripts (only for A10 / A11). Again, I will refer to my captive portal provider list for more info in case you're not skipping this.
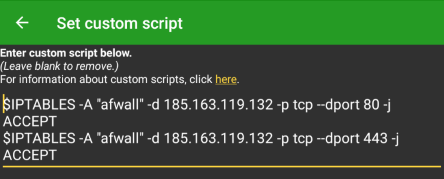
Tap the 3 dot button, & select Set custom script. Then, depending on your Android version & AFWall version, follow either of these:
Android 10 & 11; AFWall+ > 3.1.0 (8/12/2020 update : Accidentally tried without these scripts & it just works on A10. 18/1/2021 update : Tried connecting without scripts on A11 too & it works too, so I'll keep the scripts here just in case it's necessary):
Output example using /e/'s captive portal provider:
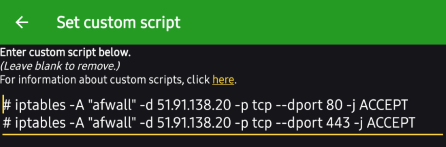
Android 9/Pie; AFWall 3.1.0 only :
Output example using Mike Kuketz' captive portal provider:
Finally, after selecting the apps you'd want to block & enabling the captive portal script (for those who use captive portal), we can finally enable AFWall+ by selecting Save (to save the app rules), then selecting Enable firewall from the 3 dot menu. Now, we wait & see if the iptables rule were applied correctly. If it stops in the middle of applying, you might want to check the custom script for any typos & such.
If you're using AdAway, install it if you haven't. Alternatively, if you have a PrivModded PDA, you could also use its hosts file.
A disclaimer : This phase will require you to rely on someone else's hosts lists. If you're not comfortable with this, at least replace the hosts sources with your own.
Open the Magisk Manager app. Then, enter its Settings & tap on the Systemless Hosts option once, and it'll add itself as a Magisk Module, which can be seen in the Modules section. Afterwards, reboot to activate the module.
This step is especially important for any device that reboots to recovery when its hosts file got changed. It could also be important if you don't want a SafetyNet failure & you're running a Pixel ROM (which I will never recommend).
Case example : I copy / pasted a hosts file from a Pie device (V30) to the Zenfone 6, & it worked. However, the same couldn't be said for the F1 (running an A10 ROM w/ A10 vendor/firmware, Official TWRP 3.3.0.0), where it triggers RescueParty, forcing me to reflash. On both, I set the permission to 644 (or 0644) in TWRP.
28/9/2020 update : Tried using systemized hosts on F1 (crDroid 26/9/2020 build, A10 vendor/firmware w/ Reignz TWRP 3.4.0-R3.1), & it somehow worked. I'm not sure what makes this work.
28/11/2020 update : Adding the OnePlus 3(T) as an example of a PDA that don't work with systemized AdAway. To apply AdAway, either use the hosts from another PDA (steps found below) or use systemless hosts here.
19/2/2021 update : In a retcon to 28/11/2020 update, systemized AdAway 5.3.0 worked on OnePlus 3(T).
Open the AdAway app. If you're using AdAway 4.3.x; it'll ask for telemetry access on startup, which you can opt out of. Root access will be prompted once you enter Preferences.
If you're using AdAway 5.1.0, it will ask for root / VPN access on the setup wizard. Grant it root access. Then, on the next step, it will attempt to download & apply the default hosts, which will fail if you haven't connected to the internet. This is fine, close & re-open the AdAway app, & you should be on the main user interface.
Either way, in Preferences (in AdAway 5.1.0 & above, Preferences > root-based ad blocker), tick "Enable IPv6"; change the Redirection IPv4 from 127.0.0.1 to 0.0.0.0 & Redirection IPv6 from ::1 to ::. If you're running AdAway >=5.1.0, you can also optionally disable automatic updates in Preferences > Automatic updates & unticking everything there. As for 4.3.x, automatic updates can be disabled by unticking Check for updates in Preferences.
Enter the Hosts sources section in AdAway. By default, AdAway will use these 3:
These hosts are, by default, for blocking ads (StevenBlack Unified also blocks some big corpo telemetry). But, as this is meant to improve our privacy, let's add these hosts:
This blocks Go-ogle's Play store, NTP, GPS, & captive portal URLs, as well as Qualcomm's IZAT & Lineage & SD Maid's telemetry. If you're using Aurora Store, whitelist play.googleapis.com & play.google.com.
This blocks Mozilla's services, such as network location, telemetry, & Pocket for Firefox. If you're using Mozilla UnifiedNLP, whitelist location.services.mozilla.org.
Blocks connections to Microsoft. Might be unnecessary since Android doesn't generally have Microsoft telemetry (Android apps built by Microsoft may have those), but perhaps a nice addition if you don't want anyone connecting to Microsoft telemetry.
In order to simplify typing them in the future, create a backup. Select the 3 dot menu, select "export backup", & grant it storage access permission. Afterwards, if you'd like to add the hosts above, you can simply use the Import backup option, and select the adaway-backup.json. For AdAway >=5.1.0, it's Preferences > Backup/restore block rules - no storage permission required.
After entering your hosts sources, connect to the internet. Then, return to the Home section in AdAway, and select "enable ad-blocking". Now, all we do is simply wait as the hosts file is applied (4.3.x). As for 5.1.0, press the reload button to check for updates, & download button (the button below the reload button) to download & apply the hosts. The more hosts used & the heavier they are, the longer the downloading & parsing will take.
Once completed, you will be prompted to reboot. Now, you can disable the internet again, & reboot to recovery to wipe Dalvik & cache, or just straight up reboot. Either way, this activates the hosts file.
This step is only meant to be done if :
Actions for the already PrivModded PDA:
Actions for the PDA about to be PrivModded:
List of devices tested with this approach (Systemized hosts approach only):
Finally, we're done in setting up our private device. Now, all that's left to do is to install & restore whatever apps you use.
Though since I did mention MyAndroidTools & SD Maid in the requirements section, let's use them in the Cleanup phase.
First, let's kick off the cleanup step by setting up a lock screen, which can be done in Settings > Security > Screen lock. Then select either Pattern, PIN, or Password, & go to town. Optionally, you could also register your fingerprint after setting up a screen lock.
If your PDA is manually encrypted / lacks the encryption mechanism found in the likes of Pixel XL / Zenfone 6, you will also have a Secure start-up prompt that you can optionally enable. This will render TWRP unable to read your data. As for those with Pixel XL's encryption mechanism, applying a screen lock will also render TWRP unable to read your data, but without the Secure start-up mechanism.
Back to top